The Aadhaar card has been under a lot of public scrutiny recently. This is because of the recent revelation that the data can be bought for just Rs. 500. However, the UIDAI also gave out a statement refuting all the allegations.
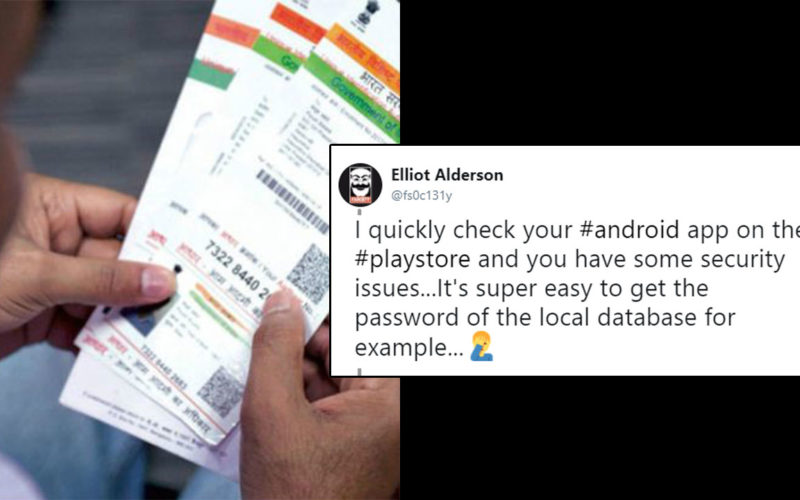
In another attempt to prove how low the Aadhaar card security is this online researcher tried something else. Going by the name of Elliot Alderson he brought to light that the mAadhaar (the official Android app for Aadhaar) has poor security standards.
Hi #Aadhaar 👋! Can we talk about the #BenefitsOfAadhaar for the #India population?
I quickly check your #android app on the #playstore and you have some security issues…It's super easy to get the password of the local database for example…🤦♂️https://t.co/acjp6tUjqs
— Elliot Alderson (@fs0c131y) January 10, 2018
He illustrated each point he was trying to make with a code he had used to hack the system.
He further said that they are “saving your biometric settings in a local database which is protected with a password. To generate the password they used a random number with 123456789 as seed” and use way too easy passwords to protect vital information.
The #Aadhaar #android app is saving your biometric settings in a local database which is protected with a password. To generate the password they used a random number with 123456789 as seed and a hardcoded string db_password_123 🤦♂️ pic.twitter.com/Ty7cPmOjAb
— Elliot Alderson (@fs0c131y) January 10, 2018
Now I’m no expert but even I can understand that this is definitely not the best safeguarding strategy. Maybe not keep a password like “123456789” for what is the largest biometric database in the world?
He even explained everything the Aadhaar card database contains. And tagged the UIDAI calling them out for their poor security measures.
So @UIDAI you are storing a biometric data on the local database: the photo of the user.
— Elliot Alderson (@fs0c131y) January 11, 2018
However, the UIDAI responded to the user and clarified that the “question of biometrics doesn’t arise” because the mAadhaar doesn’t “capture, store or take any biometric inputs”.
mAadhaar uses a local db to store the user preferences on the user's device. This data is application preferences as created by user on his/her phone. The app does not capture, store or take any biometric inputs. So question of biometrics being compromised does not arise.
— Aadhaar (@UIDAI) January 11, 2018
Elliot then tried to prove his point by replying to the UDAI.
Hi @UIDAI,
As said in this tweet, you stored the hash of the user password in the database. As the db password is identical for everybody it's easy for an attacker to get it an so compromised his account.
Can you consider this and fix that?Regards,https://t.co/vsidqAyqis
— Elliot Alderson (@fs0c131y) January 11, 2018
While companies like Facebook and Google offer bounty to anyone who can hack their platforms and report it to them, it’s the denial of the Aadhaar authorities that’s alarming. No system is full-proof, but with the help of white-hat hackers like Elliot (and hundred others), the least UIDAI can do is to acknowledge gracefully and fix the loopholes.