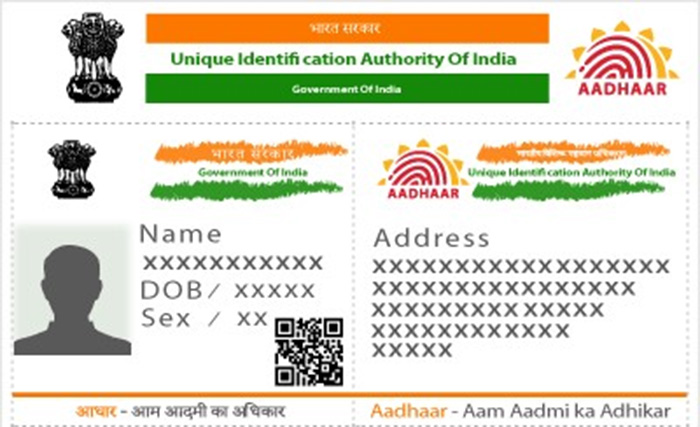
The Indian government is hell-bent on having its citizens link their Aadhaar cards, which is the Indian unique identity card, to practically all accounts possible, starting with bank accounts to mobile phones. After the recent knowledge that the database can be bought for ₹500, Elliot Alderson, an ethical hacker recently showed us how poor the Aadhaar Android App’s security really is.
This time, Elliot is back with some new information to warn us about the application’s awful security system. In a series of tweets and two videos, he explains just how easy it is to bypass the security system of the app, have access to the local database which includes the user’s biometrics too.
1. He first started by posting a screenshot of a test app named ‘NewTest’ posted on the Google Playstore by UIDAI
Hi @UIDAI 👋! Do I have to explain you how real #Android developers are working?
On his official #Playstore account. @UDAI published today an app called "NewTest" with blank screenshot and testingtestingtesting[…] as description 🤦♂️#AadhaarFail pic.twitter.com/e0iRWeesBd
— Elliot Alderson (@fs0c131y) January 14, 2018
Who does that?
2. There are multiple such ‘unreleased’ test apps released on Playstore. Oh the irony! UIDAI, why?
They also have a 3rd app called "testBeta (Unreleased)" 🤦♂️. Yes, they called an "Unreleased" an app released on the PlayStore 🤦♂️…@UIDAI maybe your interns can read this link https://t.co/O9p6SuZZgN to know how to set up an alpha/beta tests… pic.twitter.com/cN3B2JkGpW
— Elliot Alderson (@fs0c131y) January 14, 2018
3. Then he throws up an interesting challenge to UIDAI: please show us you still can update the official app.
Regarding how they used their #PlayStore account, I'm pretty sure they are unable to update the official #Aadhaar #android app because they lost the release key. Please @UIDAI, show me I'm wrong
— Elliot Alderson (@fs0c131y) January 14, 2018
App owners need a release key to push updates and Elliot is almost sure UIDAI has lost it. (gettit?)
4. Elliot isn’t wrong to claim that
.@UIDAI shame on you, you don't even have the level for a school project
My #Indian friends, good luck, these guys have no idea of what they are doing…— Elliot Alderson (@fs0c131y) January 14, 2018
5. Why do we have a self-proclaimed ‘bad coder’ coding an app for a document which is supposed to be REALLY important?
The developer section of the "NewTest" app refers to https://t.co/lUwSSVF8WI. @rrefw you have a very good description on your #github
"A pretty bad coder. I try my best though. I need to test stuff before I push. ,-," pic.twitter.com/TnyRHpUS7N— Elliot Alderson (@fs0c131y) January 14, 2018
6. Then comes the main stuff – Video 1 where Elliot shows how easy it is to bypass the password protection of the Aadhaar app under a minute
Hi my #Indian friends ?! Let me show you how to bypass the password protection set up by @UIDAI and @KhoslaLabs in the #Aadhaar#Android app.
In less than 1 minute, an attacker can access your #Aadhaar informations without having your password #AadhaarFailpic.twitter.com/ONkrbfiNbK— Elliot Alderson (@fs0c131y) January 15, 2018
Which basically means that if someone gets hold of your phone and their intentions aren’t quite good, they might crack open your Aadhaar within a minute.
7. Then comes Video-2 which showcases how easy it is to extract all the info from the database
Why is it a problem to use the same password for everyone to encrypt a database? If an attacker gets your phone, it only takes a minute to get the contents of the database#Aadhaar#AadhaarFails#GoBackToSchoolpic.twitter.com/XOm4yD5exF
— Elliot Alderson (@fs0c131y) January 14, 2018
UIDAI or Khosla Labs, the company developing the application, both are yet to comment on this glitch in their system.
.@UIDAI and @KhoslaLabs didn't make an official answer to my tweets but they definitely following me on Twitter 😂. Few minutes after this tweet, they deleted their "NewTest" app https://t.co/C1orM94zLM https://t.co/uYCOlTtkLK
— Elliot Alderson (@fs0c131y) January 14, 2018
While UIDAI have deleted the test apps and are definitely following (passive following tbh) Elliot on Twitter, they couldn’t muster the gentlemanly courage to say, “Thank you, Eliiot, for pointing our grave mistakes and helping us by identifying bugs. Here’s a bug reporting page where if you successfully break our code, we offer you rewards.”
Is it that hard to gracefully acknowledge?